Proxy servers and Liberator
This page provides guidance on hosting Liberator behind a proxy server and connecting to Liberator from behind a proxy server.
Connecting to Liberator from behind an HTTP proxy server
We recommend that clients behind HTTP proxies use HTTPS to connect to Liberator.
Using HTTPS is important not only for security, but also because it changes how traffic passes through the proxy. In HTTP communication, the proxy acts as an intermediary; in HTTPS transactions, the proxy commonly acts as a tunnel.
Tunnels are the optimum way for clients to establish a streaming connection to Liberator via a proxy. When a proxy acts as a tunnel, it is no longer considered a party in the communication between client and server. The proxy blindly passes traffic between the client and Liberator.
| Some proxy servers can be configured to act as an intermediary in HTTPS communication, also known as TLS 'bumping'. If clients behind such a proxy cannot connect to Liberator using HTTPS, connectivity may be achieved if the proxy administrator can configure the proxy to serve CONNECT requests to Liberator by HTTPS tunnel. |
Hosting Liberator behind a reverse proxy server
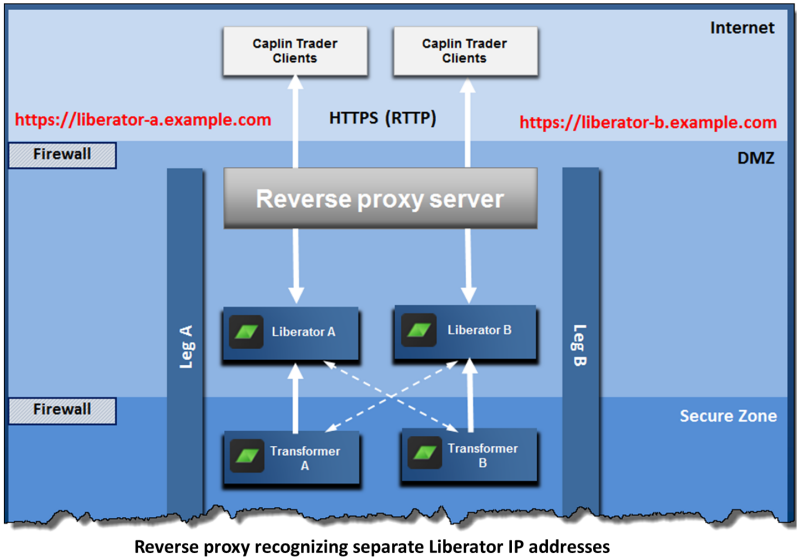
When Liberator is hosted behind a reverse proxy server, we recommend that the reverse proxy is configured so that it recognises each Liberator as having a different IP address / hostname, rather than treating all Liberators as having the same virtual IP address / hostname. This allows the StreamLink library in the client to address each Liberator separately. See the following diagram, where the two Liberators have virtual IP addresses liberator-a.example.com and liberator-b.example.com respectively:
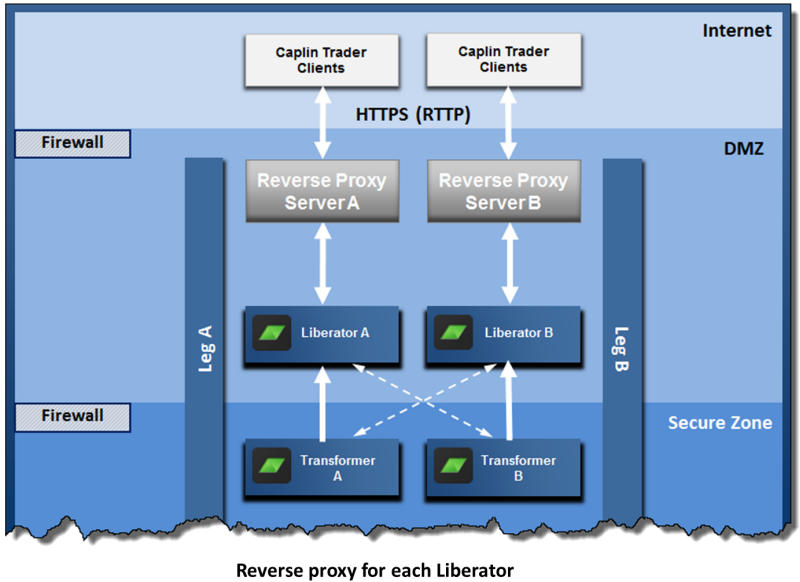
Alternatively, install a reverse proxy server for each Liberator, as shown in the following diagram. Each proxy server has a different IP address, which is the virtual IP address of the single Liberator behind it.